Aids Info Disk: a playthrough of the first-ever ransomware
A mad scientist. A deadly virus. Sex. Trendy electronic gadgets. All the ingredients for a great feuilleton are there.
Antonio Casilli, Dr. Popp et la disquette Sida1
Introduction
During my research about QuickBASIC 3 I stumbled about the story of one of the oldest and weirdest pieces of trojan malware: the AIDS Info Disk, also known as “PC Cyborg Trojan”.
The topic is fascinating. I could write a 10-page article about the story of the virus and of its author, but there are two excellent writings taking care of these topics, and most of what I’ll write will just be a blander rehash of what they say. So I will first start by giving you my sources, and recommending you to have a look at them. They are the sort of essays that make you say “I don’t even care about the topic but I’ll follow anyway because how good the author is at telling the story”.
- For the malware analysis, my reference is the file
aids.tech.info2 authored by Alan Solomon, Barry Nielson and Simon Meldrum. The first author was the creator of the famous Dr. Solomon’s Anti-Virus. - For the history of the case I took most of the material, including the quote that opens this article, from an essay1 by Antonio Casilli, professor of Sociology at the Polytechnic Institute of Paris.
You can read those writings and then skip to the section “Reviving the fossil”. For those who have less time I will instead summarize here the key points.
The AIDS Info ransomware, published in December 1989, presents itself as a program offering information about the acquired immunodeficiency syndrome. The installer would copy such program onto the victim’s hard disk, but would also replace the AUTOEXEC.BAT so that, at every boot, a secret counter would tick. At the 90th boot, the malware would trigger and encrypt the names of all files on the PC. At the same time the user would see a message stating that the PC contents had been rendered unusable, to ensure they pay the lease fees to the program’s author: they had to send a 189$ cheque for to a P.O. box in Panama, and they would get back a secret key that would decrypt the disk.
The essay by Solomon et al. includes an analysis of the license, which indeed warns the user that by using the AIDS Info program they are accepting to pay untold licensing fees, and that failing to honor this obligation will result in the computer being rendered unusable. As the authors comment, “So the subsequent demands for money - are they blackmail, or are they debt-collection? It may require a court case to decide”. Never more will I compain about modern EULAs.
Enter Dr. Popp
The company to whom the 189$ were to be paid was named “PC Cyborg Corporation”. This was just a façade for the person behind the scheme, a man named Joseph Popp. So who was him? Not the person you would imagine writing a trojan, that’s for sure! Dr. Joseph Lewis Andrew Popp Jr. III was a biologist with a Ph.D. from Harvard University in 1979. After his graduation he worked in Africa with the AMREF Flying Doctors, a group providing aeromedical assistance. Following this, he collaborated with World Health Organization in the role of advisor on the development of software for AIDS prevention. It was while working at the WHO, during the years 1988–1989, that he developed the malware: he combined the bait, a medical questionnaire for assessing the AIDS risk, with a trojan algorithm of his ideation.
After preparing the ransomware, Popp distributed it in a very old-style way: he prepared about 20,000 physical copies and sent them by mail to researchers in in 90 countries, their addresses taken from the lists of attendees to the IV International Conference on AIDS and of subscribers to various magazines.
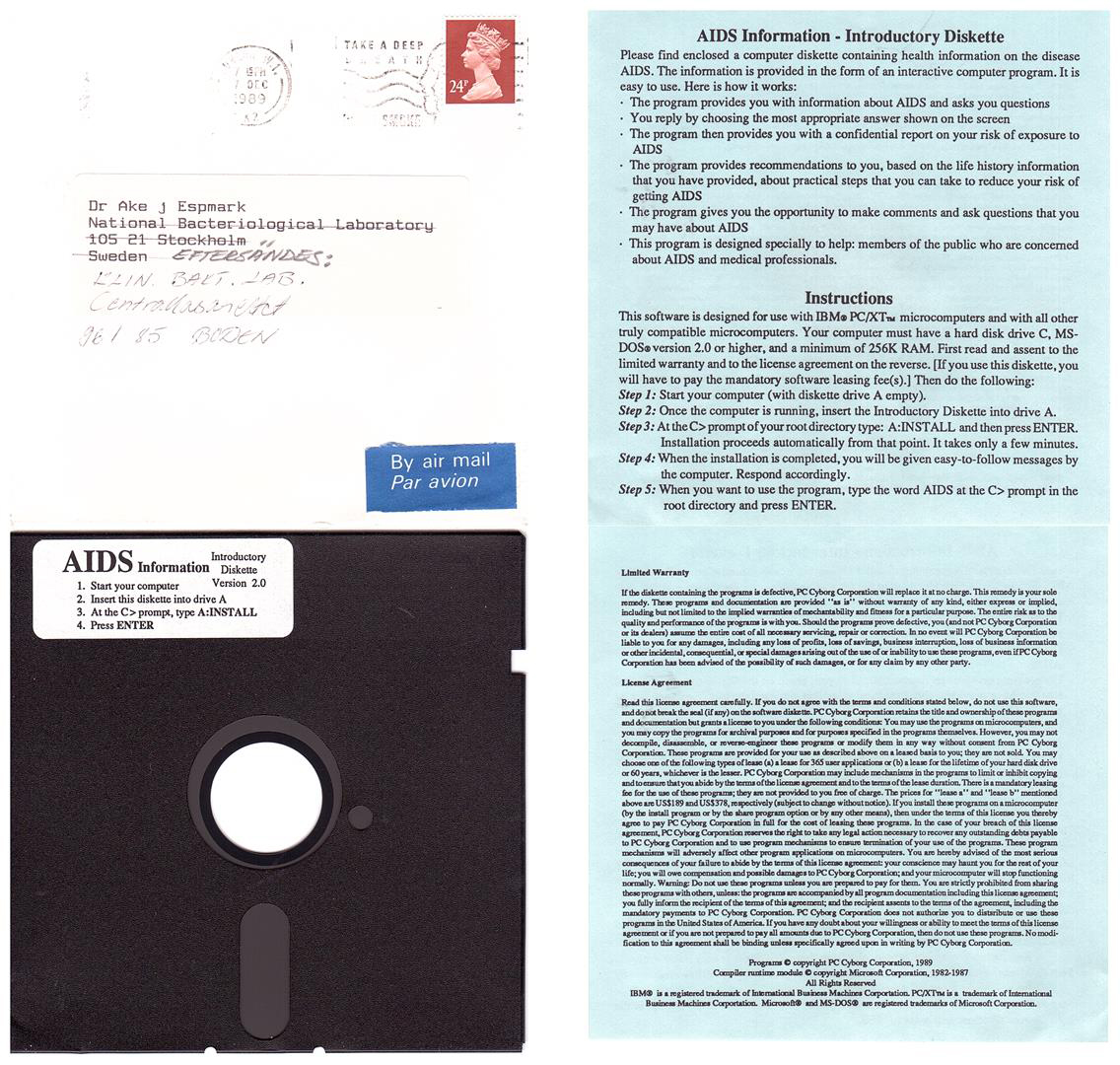
Credits: Olle Gustavsson, CC BY-SA 4.0, via Wikimedia Commons
Popp was unmasked as author when he was caught at the Amsterdam-Schiphol Airport in a state of delirium. The security officiers searched his suitcase, which contained an incriminating stamp of the “PC Cyborg” company. Still, he was let go, and only after many days in the U.S. he was arrested again and extradited to the United Kingdom. Imprisoned in Brixton, he confessed, but claimed to have plotted his extortion scheme just to raise money for research on HIV. Following various psychotic episodes, he was declared unfit for a trial and returned to the U.S. He incredibly managed to avoid further time in jail: an Italian court condemned him to a 2½-year sentence, but he never served it.3
Popp moved to his sister’s house and kept a low profile. His post-scandal works are a self-published book whose Amazon listing gets 0 reviews and 0 copies (“maximizing reproductive success is why we are here”), and a butterfly conservatory whose Tripadvisor entry scores 3.6 stars.
All this is a very condensed version of Popp’s biography. In addition to it, the article by Casilli presents a detailed reconstruction of the investigation by Scotland Yard, a reflection about Popp’s possible motives and some context about the relationship between medicine and computer science at the time. The article is clearly informed by the neo-Marxist critical theory, which may or may not be your cup of tea. Whatever its validity, I would argue that mainstream methodologies would encounter more problems in explaining Popp’s person and actions. Then again, maybe he was really just a person who had lost his mind.
Reviving the fossil
If the ransomware and the person behind it have been researched in such detail – and I have not even mentioned the 40-page analysis published by Virus Bulletin4 ! – what is the purpose of this post? Well, I had a curiosity that none of my sources managed to satisfy: how did this purported “AIDS questionnaire” look like, exactly? Was it a legitimate thing or just a cheap bait? The only way to know was to experiment in person.
Locating the content of the disk took some time, but fortunately a copy was made available by “The Virus History Project”, a creation of Snorre Fagerland, to whom I am grateful. The entry about AIDS Info Disk stores the trojan in a harmless form, the two executables renamed to prevent accidental execution. With the help of the technical reports it was easy to restore the original names, and put the content in a virtual diskette to be mounted by DOSBox.
$ ls drive-a -l
total 316
-rw-rw-r-- 1 albi albi 172562 2026-03-01 02:44 AIDS.EXE
-rw-rw-r-- 1 albi albi 146188 2026-03-02 22:19 INSTALL.EXE
As old as it might be, the trojan is still dangerous if manipulated without care. To avoid damage, I created an empty directory representing my virtual drive C. Then it was time to put myself in the shoes of an unaware medical researcher in early 1990:
dosbox-debug -c "config -set cpu cycles=350" -c 'mount a ./drive-a' -c 'mount c ./drive-c' -c 'a:'
I launched the installation program. On DOSBox-X, it failed. Vanilla DOSBox had better luck and successfully completed the install but, after that, the experiment went awry. For unknown reasons – maybe I should have populated the hard disk with fake system files? – the malware triggered immediately. After a brief “Installing…” screen, I got this message:
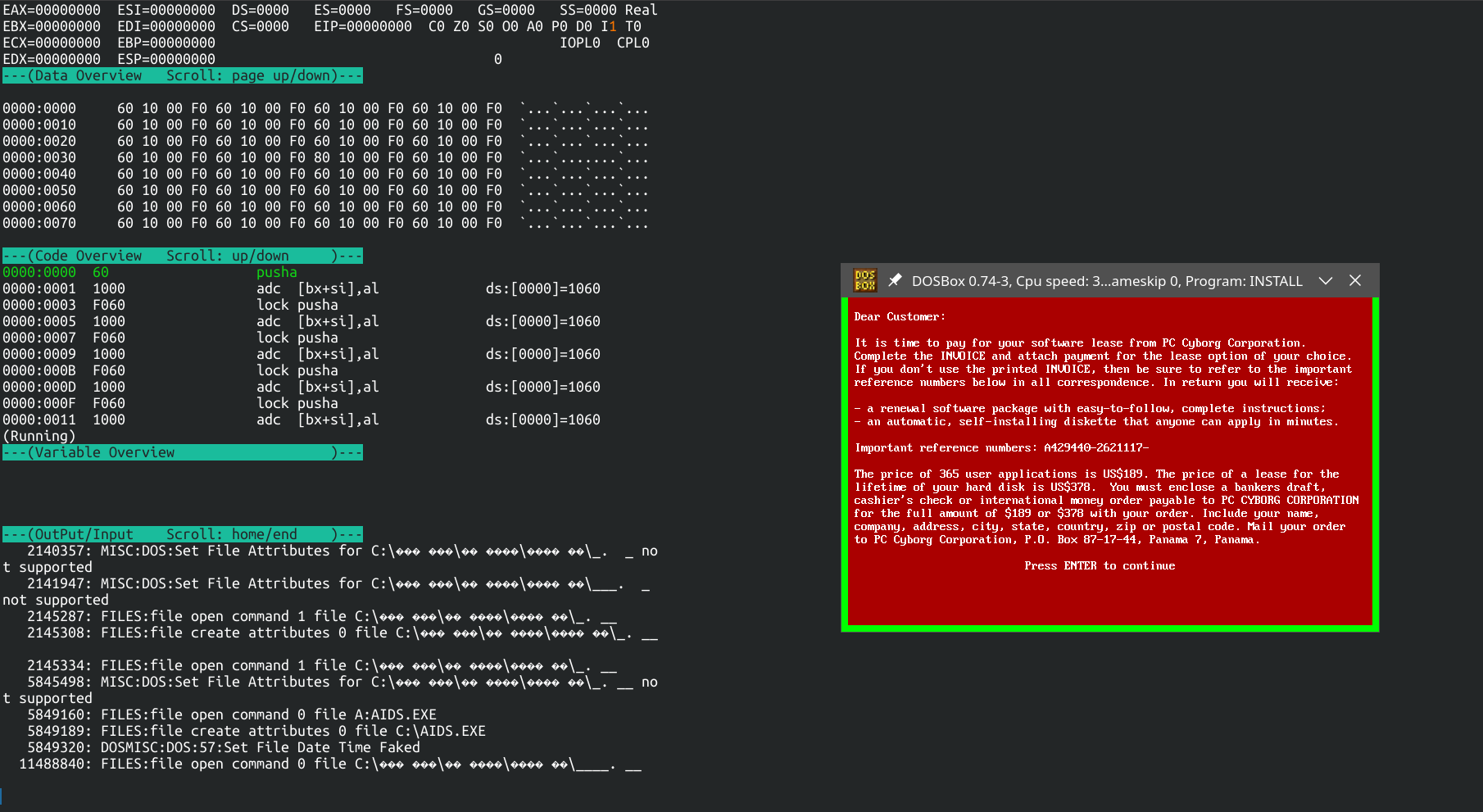
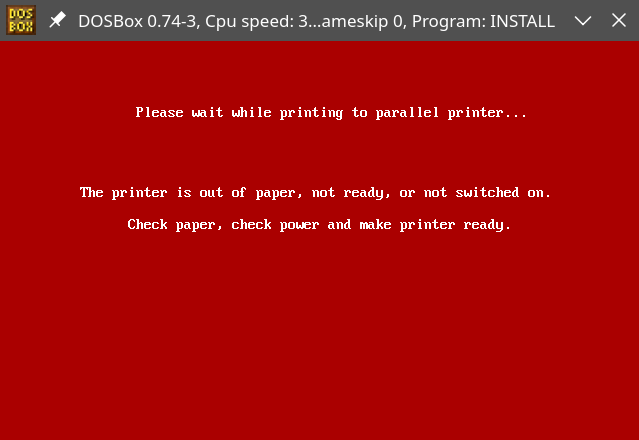
After pressing a key, the malware demanded I switched on a printer. Connecting a modern wireless laser would have ruined the atmosphere, and my old Epson LQ-500 was not at hand, so the evil plan of Dr. Popp was foiled by the lack of hardware.
This should not have happened, the red screens should have been triggered only after 90 boots. However, this was just a minor disappointment, since otherwise the installation had succeeded and had left in the virtual HDD the very directory tree described in the article by Solomon et al.:
$ tree -s drive-c
[ 4096] drive-c
├── [ 4096] \377
│ └── [ 146188] REM\377.EXE
├── [ 4096] \377\377\377\377\377\377
│ └── [ 4096] \377\377\377\377\377\377
│ └── [ 4096] \377\377\377\377\377\377
│ ├── [ 7] _._
│ ├── [ 50401] _.__
│ ├── [ 1] ___._
│ ├── [ 18] ____.__
│ └── [ 4096] ERRORIN.THE
├── [ 172562] AIDS.EXE
├── [ 98] AUTO.BAT
├── [ 17] AUTOEXEC.BAK
└── [ 108] AUTOEXEC.BAT
6 directories, 9 files
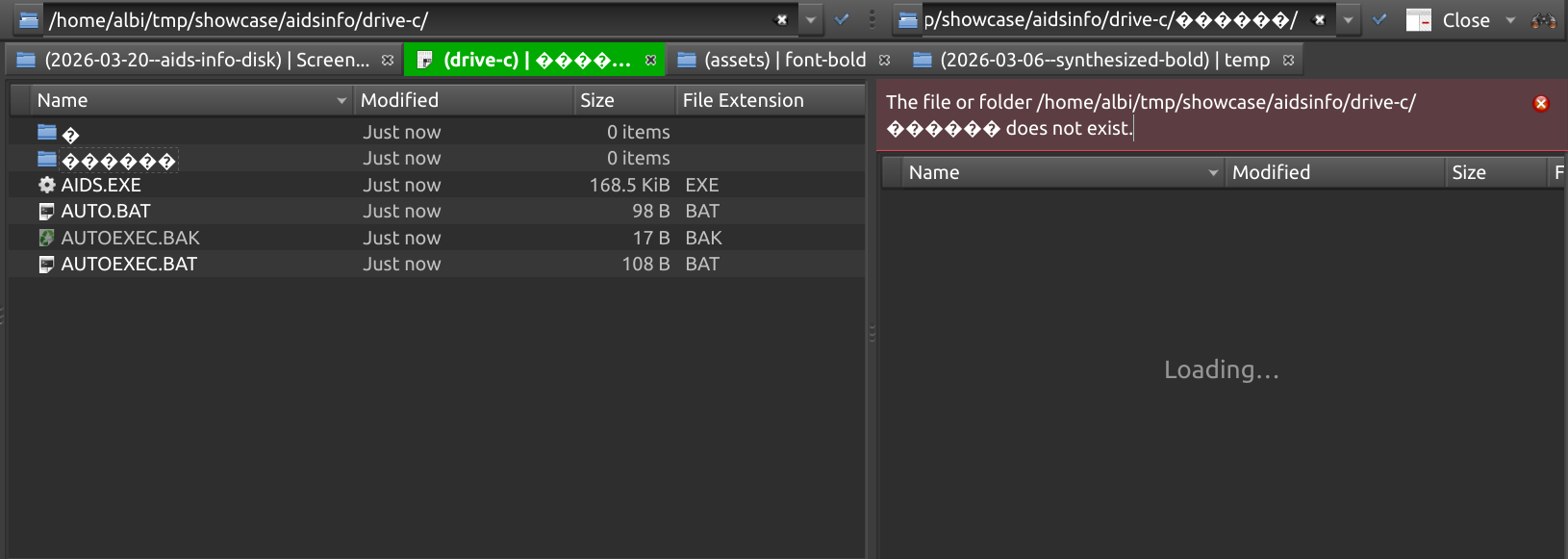
Incredibly, DOSBox managed to withstand the abuse by the malware and replicate the structure, full of special characters, on my ext4 partition. Typing the names of the directories was hard, but by judicious use of the Tab key I could navigate the drive, both in DOSBox and in native Linux:
drive-c$ cd $'\377' # entering one of the directories created by the program drive-c/\M-^?$ # Note that \377 = 255, which zsh displays as 128 + 127 == Meta + DEL == M-^?
The poor Dolphin file manager had instead to give up:
The playthrough video
After the installation, the AIDS info program could be launched. Let’s find out how it looks like.
Very professional, and possibly helpful. According to the experts consulted by the British police, “it was accurate, relatively up-to-date, with very specific information that had come to light very recently”. It looks carefully made indeed; apart for the fake progress bars there is not much to criticize.
In the part where the user can write free text, the program simply scans the input looking for keywords to match. It’s a trick as old as Eliza (1965), but it reminds me more of those text adventures where you have to guess the right verb to get a meaningful reaction from the program.
Notice the absence of the USA in the country selection screen: Popp tried to avoid problems with the criminal authorities of his home country, and he mostly succeeded.
Conclusion
Popp died in a car accident in 2006. I wish I could wring a moral out of his story, but there seems to be none. Whether he was a victim of his mental problems, or a person ready to ignore ethics to accomplish his goals, we will never know. Antidotes to his malware were quickly found, since the naive cryptography it used could be reversed. But, nonetheless, the ransomware managed to destroy the content of many computers, including years of work of several researchers. I like to think that his questionnarie has saved some lives, giving useful hints to people at risk. But, I know, it is unlikely.
I hope the reading was interesting. Take care, and don’t accept floppy disks from strangers.